Threat intelligence analysts predict and mitigate cyber threats by analyzing data, understanding attacker behavior, and creating actionable insights. Starting out in this field comes with challenges like managing overwhelming data, navigating attribution complexities, and translating findings into practical actions. Here's what you need to know:
- Key Skills: Learn network security, malware analysis, and log analysis. Tools like SIEM platforms (e.g., Splunk), EDR tools (e.g., CrowdStrike), and frameworks like MITRE ATT&CK are essential.
- Managing Data Overload: Use Priority Intelligence Requirements (PIRs) to filter relevant threats and streamline triage processes to classify alerts effectively.
- Attribution Challenges: Focus on attacker behavior (TTPs) rather than pinpointing specific groups. Use structured techniques like Analysis of Competing Hypotheses (ACH) to reduce bias.
- Actionable Intelligence: Tailor findings to stakeholders - executives, SOC teams, and IT teams - ensuring insights lead to practical defensive measures.
- Professional Growth: Gain certifications (e.g., CompTIA Security+, GIAC GCTI), build a portfolio with hands-on labs, and engage with the cybersecurity community to stand out.
Starting as a threat analyst requires technical skills, clear communication, and continuous learning. Focus on building expertise, streamlining processes, and delivering actionable insights to grow in this dynamic field.
Zero to CTI: A Novice’s Journey into Threat Intelligence
sbb-itb-8a31326
Managing Information Overload and Setting Threat Priorities
5-Step Process for Building Effective Priority Intelligence Requirements (PIRs)
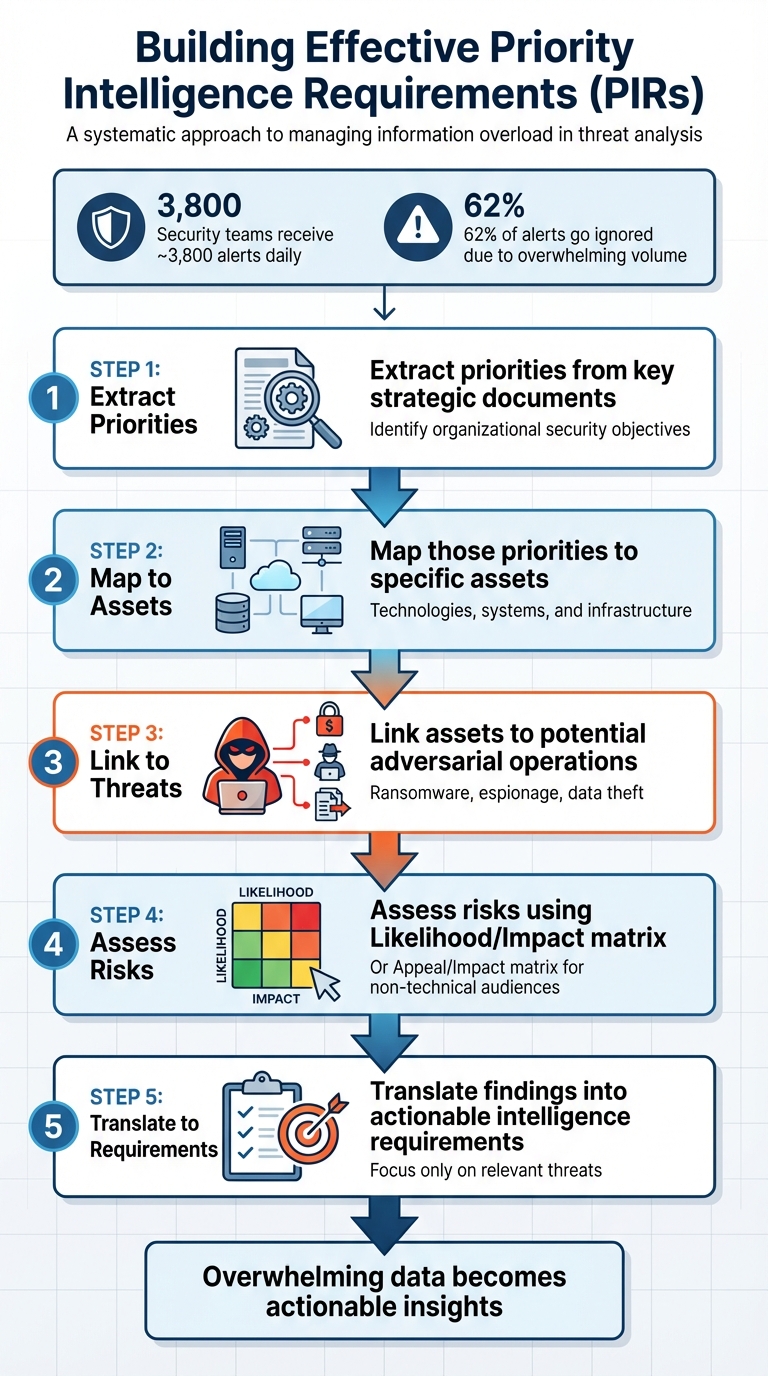
One of the biggest hurdles for new analysts is the sheer volume of information they face daily. On average, security teams are bombarded with around 3,800 alerts each day, and roughly 62% of these alerts go ignored - simply because there’s too much noise to sift through. This isn’t about lacking skills; it’s about being overwhelmed by the sheer quantity of data. Addressing this requires a systematic approach.
The solution lies in Priority Intelligence Requirements (PIRs). This structured framework helps organizations focus on what truly matters. Instead of chasing every threat that pops up in global feeds, PIRs encourage teams to ask critical questions like, “Does this threat specifically target our industry, assets, or technology stack?” By narrowing the scope, teams can allocate resources effectively, balancing proactive strategies with the need to respond to immediate threats.
Defining Intelligence Requirements
Intelligence requirements act as a filter, ensuring only relevant data makes it to your desk. The key is to set clear objectives in collaboration with stakeholders, ensuring every piece of data serves a specific purpose. Here’s a practical five-step process to build effective PIRs:
- Extract priorities from key strategic documents.
- Map those priorities to specific assets, such as technologies or systems.
- Link assets to potential adversarial operations, like ransomware or espionage.
- Assess risks using tools like a Likelihood/Impact matrix or an Appeal/Impact matrix for non-technical audiences.
- Translate findings into actionable intelligence requirements.
This approach eliminates the temptation to track everything. By ruthlessly filtering out irrelevant data, you can focus exclusively on intelligence that aligns with your organization’s threat profile. The result? Overwhelming data becomes actionable insights, providing a solid foundation for triage.
Creating Triage Processes
Once intelligence requirements are in place, the next step is categorizing incoming alerts efficiently. Triage isn’t about rushing - it’s about consistency. A reliable triage process helps classify alerts into three categories: Benign (not a threat), False Positive (triggered by detection errors), or True Positive (malicious activity).
Start by verifying the trigger behind each alert before diving into logs. For instance, when dealing with endpoint alerts, always check if the suspicious file or process was actually executed. Artifacts like Prefetch or Shimcache can confirm execution and prevent unnecessary escalations.
Prioritization should consider the value of the assets involved. Focus on critical assets and their potential impact. For example, an authentication anomaly on a domain controller demands immediate attention, unlike a similar alert on a test server.
A standardized checklist can also help streamline investigations. For example:
- For authentication anomalies: “Was Multi-Factor Authentication (MFA) used?”
- For email-related alerts: “Did the user interact with the attachment?”
This structured approach reduces the mental strain on analysts, ensuring they consistently ask the right questions and make informed decisions.
Separating Noise from Critical Signals
Alerts alone only tell part of the story. Context is essential. For example, an IP address is just a number until you enrich it with details like ownership, past activity, and current behavior.
"Alerts tell you that something happened. Threat intelligence tells you who, why, and what comes next." - CyberDefenders Team
Fine-tuning alert thresholds can also help reduce false positives. Instead of triggering an alert for a single mistyped password, configure it to activate only after several rapid failed login attempts. This adjustment cuts down on noise while still catching genuine threats.
Triage should function as a feedback loop. If an alert consistently proves to be a false positive, it’s worth tweaking or suppressing it to minimize future noise. Clear documentation during investigations is equally vital - it not only sharpens your thinking but also highlights gaps in your logic.
Automation can further ease the burden of repetitive tasks. Tools like Security Orchestration, Automation, and Response (SOAR) can automatically ingest threat feeds and block malicious IPs with high confidence. Similarly, scripts in Python or PowerShell can handle data parsing and collection, freeing up time for analysts to focus on deeper, more strategic work. The key is to automate routine tasks while reserving human judgment for understanding attacker behavior and assessing organizational impact.
Attribution Difficulties and Building Analytical Confidence
New analysts often face significant challenges with attribution, a critical yet complex aspect of cybersecurity. Attribution involves identifying the perpetrators behind a cyberattack, and it’s far from straightforward. Attackers frequently use deceptive tactics, such as deploying false flags that mimic other threat groups, adopting shared infrastructure like bulletproof hosting services or VPNs, and exploiting compromised servers. With data often incomplete, attribution feels more like piecing together a mosaic than solving a clear-cut puzzle.
However, pinpointing the exact attacker isn’t always necessary. Instead, the focus should shift to understanding attacker behavior, which can lead to stronger defenses. As Intel 471 explains:
Attribution should be presented in terms of a balance of facts and evidence against opposing evidence, known intelligence gaps, and blind spots.
Rather than fixating on identifying a specific group, analysts should prioritize behavioral patterns - Tactics, Techniques, and Procedures (TTPs) - which are much harder for adversaries to conceal. This nuanced approach to attribution lays the groundwork for employing structured methods that enhance analytical confidence.
Using Structured Analytical Techniques
Structured methods like the Analysis of Competing Hypotheses (ACH) help analysts evaluate multiple possibilities while reducing bias. ACH emphasizes a "reject-first" mindset, encouraging analysts to focus on disproving hypotheses rather than merely seeking supportive evidence. The process involves creating a matrix where hypotheses are listed horizontally and evidence vertically, using symbols like +, –, or 0 to assess alignment. The hypothesis with the fewest disconfirming "red boxes" often emerges as the most plausible. Adam Goss, Founder of Kraven Security, explains:
The seven steps are not designed to offer prescriptive advice that leads you to the 'right' decision. Instead, they provide a structure for you to follow when assessing the validity of competing hypotheses that mitigates potential biases and promotes logical reasoning.
Key steps include removing non-diagnostic evidence and documenting assumptions. If an assumption later proves incorrect, the entire assessment may need reworking. These structured techniques not only improve analysis but also facilitate clearer communication of uncertainties.
Communicating Uncertainty Clearly
Effectively conveying uncertainty is crucial for earning stakeholders' trust. Using defined probability terms - such as "likely" to indicate a 55–70% chance - helps clarify uncertainty. Confidence levels should also be transparent: low confidence signals limited data or multiple plausible alternatives, moderate confidence reflects a solid but revisable case, and high confidence indicates strong, corroborated evidence. As Deniz Topaloglu points out:
Being approximately right with caveats is preferable to being confidently wrong.
In reports, it’s essential to separate observed facts from interpretations and to highlight intelligence gaps. Explaining how missing information impacts the overall assessment ensures stakeholders understand the limitations of the analysis.
Prioritizing Actionable Intelligence
For stakeholders, actionable recommendations often outweigh detailed attribution. Providing clear guidance - such as detection strategies or defensive measures - empowers decision-making. Grouping incidents with shared TTPs for continuous monitoring can be particularly effective. Mapping adversary behaviors to the MITRE ATT&CK framework offers an objective way to compare them with known threat profiles.
Ultimately, transforming raw data into actionable intelligence is the goal. Whether it’s creating detection rules, prioritizing software patches, or refining monitoring strategies, actionable insights strengthen cyber defenses. This approach ties back to earlier discussions on triage, ensuring that effective data management and thoughtful attribution directly translate into meaningful actions.
Turning Intelligence into Action
Taking intelligence and transforming it into actionable steps is where analysis meets real-world security improvements. For entry-level analysts, the challenge lies in turning raw threat intelligence into defenses that can be implemented. Amit Gupta, Founder of Tech Magazine, explains it best:
To operationalize threat intelligence means to convert raw signals into remediation through tickets, detections, or configuration changes.
The disconnect between intelligence and action often comes from missing internal context. Generic indicators are meaningless to engineering teams unless they’re tied to specific organizational assets, technologies, or versions. This is where new analysts often face difficulties in guiding actionable remediation.
Working with Security Teams
Collaborating effectively with operations and engineering teams means learning to communicate in their terms. Provide clear, asset-specific instructions. For instance, instead of saying, "CVE-2024-XXXX affects Node.js", specify, "Upgrade the Node.js dependency in the payment-api repository from version 18.2 to 18.4".
When dealing with SOC analysts, ensure the intelligence is presented in formats they can immediately use, such as SIEM rules, EDR alerts, or YARA signatures.
To prioritize threats, focus on these four criteria:
- Evidence of active exploitation in the wild
- Presence in your organization’s technology stack
- External reachability
- Ease of remediation
This approach helps teams address the most pressing issues, moving beyond generic CVSS scores to focus on what truly matters.
Converting Findings into Usable Formats
The key to making technical data actionable lies in tailoring your outputs to meet the needs of different stakeholders. Here’s a quick breakdown:
| Stakeholder | Focus Area | Key Output Formats |
|---|---|---|
| Executives | Business risk, ROI, long-term strategy | Strategic reports, high-level summaries |
| SOC Analysts | Real-time detection, incident response | SIEM rules, EDR alerts, enriched IoCs |
| IT/Engineering | Infrastructure stability, remediation | Remediation tickets (Jira/GitHub), patch priorities |
| Threat Hunters | Proactive defense, emerging TTPs | Behavioral patterns, MITRE ATT&CK mapping |
Integrate these findings directly into existing workflows using tools like Jira or GitHub. This ensures that intelligence doesn’t get lost in emails or Slack threads.
When analyzing threat reports, ask functional questions like: What did the attacker do? Why did they do it? What telemetry would reveal this activity? Security analyst Seif highlights the importance of this approach:
If you finish a report and can't answer 'What could I detect from this?' or 'What sort of gaps in my own organization can be impacted by this?': You didn't actually read it.
Annotating reports as you read can also help. For example, note, “This is credential access via LSASS dump; requires admin; leaves file artifact here” to quickly identify necessary telemetry. This habit transforms passive reading into actionable insights.
Tracking the Impact of Recommendations
Once your findings are turned into actionable steps, tracking their implementation and effectiveness becomes crucial. Measure efficiency by monitoring how long it takes from receiving intelligence to creating tickets and from ticket creation to deployment of fixes. These metrics reveal how well intelligence is being operationalized.
Use tools like the MITRE ATT&CK Navigator to identify coverage gaps. Count how many "red" cells (uncovered techniques) turn "green" after implementing detection recommendations. This visual feedback helps demonstrate progress to leadership.
Regular feedback loops with SOC and incident response teams are another essential step. These discussions can reveal which intelligence products were helpful and where adjustments are needed. Ask teams about the ease of remediation to refine future recommendations.
Emanuel Salmona, Co-founder & CEO of Nagomi Security, summarizes the goal:
A successful threat intelligence program results in: Reduced mean time to prevent; Fewer false positives, thanks to better data prioritization; Improved visibility into real threats targeting the organization.
Finally, document everything - sources, actions taken, and outcomes. This not only builds credibility but also helps justify the value of the intelligence function within the organization.
Building Technical Skills and Tool Knowledge
To strengthen your technical foundation, dive into hands-on practice with commonly used cybersecurity tools and frameworks. These skills are essential for transforming raw data into actionable intelligence - one of the main challenges for entry-level threat analysts. Many beginners struggle to bridge the gap between theory and real-world application, but you don’t need costly courses or years of experience to make progress.
Core Knowledge Areas
Focus on mastering three key areas: network security, malware analysis, and log analysis. Understanding how networks operate, spotting unusual traffic patterns, and addressing security challenges in both wired and wireless environments are fundamental skills for threat analysis work. Learn basic malware analysis techniques - both static and dynamic - to extract indicators of compromise and identify malicious behavior.
Equally important are log and data analysis skills. Security teams often rely on logs to monitor for threats, sometimes incorporating statistical analysis or machine learning to detect anomalies. Beyond technical expertise, learning intelligence tradecraft like the Intelligence Cycle (Planning, Collection, Processing, Analysis, Dissemination, Feedback) and structured techniques such as Analysis of Competing Hypotheses can set you apart from those who just process alerts. Additionally, developing OSINT skills - gathering and connecting data from public sources, social media, and even dark web forums - can enhance your ability to provide actionable insights.
These foundational skills pave the way for practical training and certifications.
Practical Training and Certifications
Certifications such as CompTIA Security+ and CySA+ offer a strong starting point for beginners, while advanced credentials like GIAC Cyber Threat Intelligence (GCTI) or Certified Threat Intelligence Analyst (CTIA) can validate your expertise. However, certifications alone won’t secure a job - employers want proof you can apply your knowledge.
Platforms like TryHackMe, Blue Team Labs Online, LetsDefend, and CyberDefenders are excellent for building practical experience. With consistent effort, you can progress to a Tier 1 analyst role in 9–18 months if studying full time, or 18–30 months if balancing work. Candidates who pair a core certification with 50–100 completed lab exercises and maintain a public portfolio often outperform 90% of applicants.
Start learning scripting early - Python is great for automation, while PowerShell is key for Windows incident response. Familiarity with parsing JSON, using regular expressions, and writing KQL (Kusto Query Language) for Microsoft Sentinel can also be valuable. Plus, cloud security expertise could add over $15,000 to your annual salary.
Once you’ve built your skills and earned certifications, it’s time to get comfortable with essential frameworks and tools.
Frameworks and Tools
Begin by exploring industry-standard frameworks. The MITRE ATT&CK framework is a must for understanding adversary behaviors and identifying gaps in defenses. Gain hands-on experience with SIEM platforms like Splunk, IBM QRadar, or Elastic Security for log aggregation and threat detection. Familiarity with endpoint detection and response (EDR) tools such as CrowdStrike Falcon, SentinelOne, and Microsoft Defender for Endpoint is also critical.
For threat intelligence gathering, learn to use Threat Intelligence Platforms (TIPs) like MISP, OpenCTI, Recorded Future, and Anomali ThreatStream. Tools like VirusTotal, ANY.RUN, Maltego, and YARA are invaluable for malware analysis and developing detection rules. Network analysis tools such as Wireshark, Zeek, and Tcpdump are essential for spotting malicious traffic.
Set up a basic home lab with VirtualBox or VMware, including Windows 10/11 (evaluation license), Kali Linux, and Flare-VM for digital forensics and incident response (DFIR) tools. Using isolated virtual machines and tools like REMnux or Flare-VM, you can safely analyze malware samples from repositories like MalwareBazaar. Documenting your work on platforms like GitHub or Notion provides concrete evidence of your practical skills.
"The junior who writes clear, public write-ups will always beat the 'secret genius' who keeps everything private." - RootGuard
For a structured learning path, Root School offers tailored resources to help aspiring cybersecurity professionals build the skills needed to land their first role as a threat analyst.
Communicating Across Different Audiences
Being able to communicate effectively is just as essential as technical expertise when it comes to transforming threat intelligence into actionable defense strategies. As a threat analyst, your job isn’t just to process alerts - it’s to ensure your findings resonate with everyone, from executives to IT teams. Analysts who can clearly convey their insights will always stand out. This clarity becomes even more important when tailoring communication to meet the needs of different stakeholders.
Simplifying Complex Concepts
Every report should begin with a Bottom Line Up Front (BLUF) - start with the most important insight instead of saving it for the end. Avoid creating unnecessary suspense and focus on delivering the critical takeaway immediately. Follow the ABC principle: Accuracy, Brevity, and Clarity. Your goal is to go beyond simply describing what happened. Instead, answer the critical question: “So what?” Explain what the facts mean for your organization and what actions may be necessary.
A helpful tool for structuring your communication is the TIP Framework:
- Topic: What’s the subject of your report?
- Intent: Why does it matter?
- Point: What action or takeaway is required?
"Great CTI writing isn't about showing off your analysis - it's about getting the right insight to the right people at the right time." - TΞLΞMΞTRY
To make your findings accessible, replace technical jargon with standardized terms. For example, use probability metrics like "likely", "highly likely", or "remote possibility" to describe the likelihood of a threat. Be clear about the difference between Probability (the chance of an event occurring) and Confidence (how reliable your estimate is). Frameworks like the Admiralty System, which grades sources on reliability (A–F) and accuracy (1–6), can help add structure to your analysis without overwhelming your audience.
After simplifying complex ideas, the next step is tailoring the message to suit each audience’s unique concerns.
Adapting Communication for Stakeholders
Not every audience needs the same level of detail. For example, executives are primarily interested in the big picture - business risks, resource allocation, and strategic recommendations. On the other hand, security teams require technical breakdowns, such as indicators of compromise (IoCs) and attack vectors, while IT teams need actionable steps like patching requirements or infrastructure updates.
Here’s a quick breakdown of what each stakeholder group typically focuses on:
| Stakeholder Group | Primary Focus | Key Content |
|---|---|---|
| Executives | Business risk and resource allocation | High-level summaries, ROI, and strategic impact |
| Security/SOC Teams | Detection and mitigation | IoCs, TTPs, and technical attack vectors |
| IT/Operations | Infrastructure stability | Patching requirements and operational configuration steps |
| External Partners | Collaboration and compliance | Shared indicators and joint defensive actions |
When presenting technical metrics, translate them into actionable insights. For example, instead of detailing malware behavior, emphasize specific steps your organization can take to mitigate its effects. Scenario analysis is another useful tool - lay out multiple potential outcomes to encourage stakeholders to think beyond the assumption that past events will predict the future.
Building Credibility Through Clear Reporting
Clear, well-structured reports can do more for your professional reputation than any certification. When you consistently deliver accurate and concise intelligence that informs decision-making, you build trust with leadership. This trust is critical for securing support for your team’s tools and resources. Beyond professional credibility, clear reporting also enhances operational efficiency by ensuring that everyone - from executives to IT staff - understands what’s at stake and what needs to be done.
To further establish your expertise, consider documenting your work publicly. Share threat hunting techniques, contribute to open-source intelligence projects, or present at cybersecurity conferences. These efforts can demonstrate your skills and build credibility in ways that internal contributions alone cannot.
Gaining Experience and Building Professional Credibility
Breaking into threat intelligence might feel overwhelming at first, but with over 700,000 unfilled security roles in the U.S., the demand is there - you just need to show you have the skills to match.
Starting with Entry-Level Roles
Roles like SOC Analyst Tier 1 or Incident Responder are excellent starting points. These positions teach you essential skills like triaging alerts, investigating unusual activity, and tracking lateral network movements - all of which are crucial for threat analysis. In fact, most SOC analyst job postings highlight the importance of SIEM experience (90%), log analysis skills (85%), and clear incident reporting (95%). These roles are a great way to build both the technical and communication skills you’ll need to succeed.
"Threat intelligence researchers find needles in haystacks and then somehow spin those needles into gold."
- Winnona DeSombre, Threat Intelligence Researcher, Recorded Future
Creating a Professional Portfolio
Hiring managers are increasingly prioritizing proven skills over certifications. A strong portfolio can make all the difference. Aim to include 2–3 detailed case studies that showcase your investigative process. Walk through how you gathered context, analyzed data, and reached your findings, including the steps you took for mitigation or response. Platforms like GitHub, a personal blog, or even Notion are great places to host your work.
Your portfolio should demonstrate key accomplishments, such as reviewing 30+ alerts, conducting 5 vulnerability scans, building 2 SIEM dashboards, and creating 20 detection rules mapped to the MITRE ATT&CK framework. These metrics can also enhance your resume with impactful statements like "Investigated 30+ security alerts" or "Built 2 SIEM dashboards for monitoring failed logins." Including specific tools and tasks - like using Splunk, Nessus, or handling phishing triage - can boost your response rate by 2–3×.
"The portfolio was key. In interviews, I showed my GitHub and they saw I could actually do the work."
- Sarah, Junior SOC Analyst
To build your portfolio, try hands-on labs like TryHackMe’s SOC Level 1 path, HackTheBox, or EpicDetect. You can also set up a home lab using tools like Splunk Free or Nessus Essentials to practice log ingestion, dashboard creation, and detection rule development. The quality of your investigations will always outweigh tool familiarity.
While a strong portfolio is essential, connecting with others in the industry can help establish your credibility even further.
Engaging with the Cybersecurity Community
Networking plays a critical role in bypassing applicant tracking systems and getting your work noticed by decision-makers. After applying for a job, consider reaching out to a current team member on LinkedIn. Highlight your lab work and ask for a brief chat to learn how they evaluate junior candidates.
You can also expand your network by participating in Capture The Flag (CTF) competitions, attending local security meetups like BSides or OWASP, and joining professional Discord communities. Sharing your lab write-ups or findings on Medium or a personal blog can help establish your professional voice. Even passive engagement - like following industry leaders on social media or listening to security-focused podcasts - can keep you informed about trends and opportunities.
"Landing in Recorded Future as a threat intelligence researcher right out of college was my lucky break - had it not been for some great mentors and a Recorded Future advertisement in my favorite security podcast, I might not have known that threat intelligence even existed."
- Winnona DeSombre, Threat Intelligence Researcher, Recorded Future
For those just starting out, Root School offers tailored resources to help aspiring professionals land their first cybersecurity roles.
Conclusion
Starting out as a threat intelligence analyst comes with its fair share of challenges - managing overwhelming amounts of information, navigating attribution complexities, and turning insights into actionable steps. But these hurdles are part of the journey from being a technician to becoming a well-rounded analyst.
It’s important to understand that this transition doesn’t happen overnight. On average, moving from simply addressing alerts to developing a deeper analytical approach takes about 18 months. During this time, focus on getting the basics right: clearly define intelligence requirements, use structured methods like the Analysis of Competing Hypotheses, and prioritize building context over rushing through tasks. Even spending an extra 5–10 minutes reviewing historical logs or user activity can significantly improve the accuracy of your analysis.
"Skill gets you hired. Thinking makes you valuable."
- Manubhav Sharma, Threat Analyst
Continuous learning is the foundation of growth in this field. The threat landscape evolves constantly, with new challenges like AI-driven malware, cloud-specific security gaps, and IoT vulnerabilities emerging regularly. No analyst can keep up with everything, so it’s crucial to develop sustainable learning habits. Join industry-specific Information Sharing and Analysis Centers (ISACs), attend events like Black Hat or DEF CON, and learn scripting languages like Python to automate repetitive tasks.
Above all, remember that intellectual humility is a strength, not a weakness. The best analysts openly acknowledge gaps in their knowledge and communicate uncertainty effectively. Thorough documentation, fostering collaboration across teams, and delivering actionable intelligence are key to making a meaningful impact. By embracing these principles, you’ll not only enhance your technical expertise but also establish yourself as a trusted and indispensable analyst.
For those aspiring to break into cybersecurity, platforms like Root School offer practical training and resources to help you land your first role. With the demand for skilled threat analysts growing, honing your skills and staying adaptable will help you stand out in this dynamic field.
FAQs
How do I decide what to focus on first?
To kick off your journey, focus on cybersecurity fundamentals such as network security and common attack methods. Dedicate around 3–4 months to building this foundation. Once you're comfortable with the basics, spend the next 2–3 months diving into open-source intelligence (OSINT) tools and techniques, which are essential for gathering and analyzing data.
To bolster your knowledge and credentials, consider earning beginner-friendly certifications like CompTIA Security+ or Network+. These not only validate your skills but also demonstrate your commitment to potential employers. With these steps, you'll be well-prepared to take on more complex challenges in the field of threat intelligence.
Do I need to attribute attacks to a specific group?
Attributing cyberattacks to a specific group can offer important insights, such as anticipating future moves or strengthening defenses. However, pinpointing the responsible party is no easy task, given the intricate nature of cyber operations. Full attribution may not always be achievable, but even recognizing tactics or techniques tied to known groups can help prioritize threats and refine response plans. The key lies in gathering reliable, high-quality intelligence to inform and support your strategies effectively.
How can I prove impact from my threat intel work?
To emphasize the importance of your threat intelligence efforts, focus on how your insights have led to measurable improvements in security. For example, you could highlight achievements like identifying threats early, preventing attacks, or supporting strategic decisions.
Use concrete metrics to back up your claims, such as shortened response times, higher detection accuracy, or reduced risk exposure. Including case studies or detailed reports that directly connect your findings to enhanced risk management or operational improvements can make your contributions even clearer. These examples help demonstrate the tangible value you bring to the table.